Cybersecurity
Reducing Risk to Your Business
By far the biggest risk to your business today, is a cybersecurity incident. You need to protect yourself from this ever evolving, ever present threat. From bedroom hackers to state sponsored groups, everyone is a target and no-one is safe. But here’s the good news. Get this right and you’ve got yourself the best foundation on which to build your business.

A Lot Of People & Websites Talk About Cybersecurity, But
How Does That Affect You?
That’s a great question and the reason we have built our cybersecurity widget below.
If you would like to have a play, click on the item on the left that you think might be most relevant to your business.
The widget will then show you how much it would cost you if that breach occurred, how our service would stop this and give you a summary of the tools and services we use to prevent it.
You can then use the companion to then keep a log of this for you and guide you through the rest of the problems we solve.

It’s All In The Numbers
Is That Really Bad?
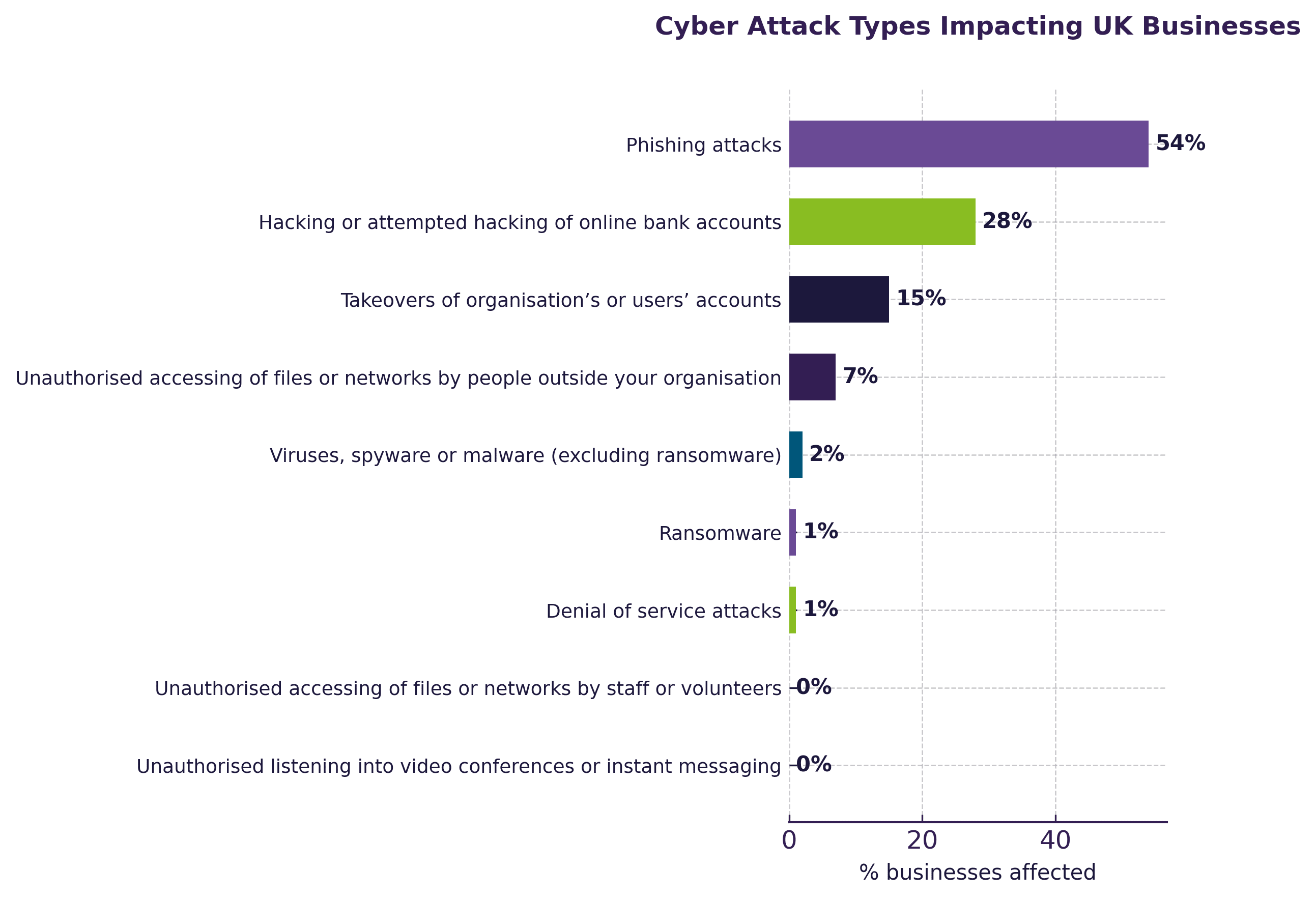
Unfortunately, statistics tell us that the single biggest risk of a security or data breach is people. Too many businesses neither see themselves as handling data or as a potential target and that complacency or lack of awareness is what hackers count on.
I know it sometimes feels like this isn’t going to happen to you, but the statistics don’t lie. We don’t want you to become one of the 30% of businesses who go under each year due to these criminals.
It’s time to act and time to understand how you can have great security that actually improves productivity.
Risk Reduction
What You’re Up Against
All it takes is simple email asking one of your staff to open a shared document. Hacks are sent out on mass, often using purposefully bad grammar as a targeting strategy to identify accounts more susceptible to link-clicking . Once a link is clicked, passwords and Muti Factor Authentication codes entered, that’s it – that account is breached and can be used to access all associated contacts and company data.
Hackers use clever techniques to bypass email security checkers – like using a link to your OneDrive to host a file which can be used to spread itself until someone with admin rights submits their details.

Advanced IT Requirements
What our customers say
“Alex was very quick on the task and also followed-up afterwards.”
It was all about getting the right systems in place for now, and I didn’t feel I was being upsold or pushed into anything. That really worked for me.
“The relationship isn’t transactional —it’s a partnership. We trust them, and they’ve earned that through consistency, communication, and real expertise.”
“As always, Jonathan redenered exceptional to our requirement. Very fast and reliable.”
“Ben was Super Excellent. He fixed my computer issue with swift and detailed expertise. He went above and beyond and fixed issues that were on my PC prior to my calling. I am so overjoyed I no longer have computer issues.”
Strategic IT Support
Resources & Articles









